70+ Modules & Real EDR/AV Labs
60–75 Hours Training
3000+ Students Trained
4.9 Rating (2500+ Reviews)
Want to bypass the most sophisticated EDR and AV solutions used by enterprises today? Our EDR/AV Evasion Techniques Training in Pune delivers complete hands-on mastery of process injection, AMSI/ETW bypass, custom loaders, kernel-level evasion, and living-off-the-land techniques. Perfect for experienced pentesters and red teamers who want the elite skills top organizations in Pune demand.
Master EDR/AV Evasion in Just 75 Days
| Course | EDR/AV Evasion Techniques Training |
| Duration | 2 – 2.5 Months (60–75 Hours) |
| Mode | Classroom (Pune) & Live Online |
| Includes | Theory, 70+ Real EDR/AV Labs, Custom Implant Development, Mock Interviews, Placement Support |
Accredited by
Quick Answer: The Best EDR/AV Evasion Techniques Training in Pune is offered at Ethical Hacking Institute in Kharadi. This advanced program covers process injection, AMSI/ETW bypass, custom loaders, kernel-level evasion, living-off-the-land techniques, real EDR/AV lab environments and dedicated placement support. Students from Kharadi, Viman Nagar, Wagholi, Hadapsar, Baner, Hinjewadi, Wakad and nearby EON IT Park gain the complete skill set needed for high-paying advanced red team and offensive security roles.






"The CEH v13 AI course in Pune gave me real-world penetration testing skills and hands-on labs that no other institute offers. Got placed at TCS within 2 months of completion. Best decision for my cybersecurity career!"

"Excellent CEH v13 AI training with industry experts. The practical labs and real attack scenarios helped me crack interviews easily. Strong placement support in Pune – highly recommended for anyone serious about ethical hacking!"

"From zero knowledge to landing a penetration testing role – all thanks to Ethical Hacking Institute Pune. The CEH v13 AI curriculum is updated, trainers are exceptional, and the projects gave me confidence to handle real client VAPT work."

"The best cybersecurity training institute in Pune! The CEH v13 AI program covered everything from basic networking to advanced ethical hacking. Placement team helped me secure a SOC Analyst role. 100% practical and job-oriented."

"Transformed my career! The hands-on labs and OSCP-level exposure in the CEH v13 AI course were outstanding. Got multiple offers in Pune’s cybersecurity market. Trainers are industry veterans – truly the best ethical hacking institute."

"I completed the CEH v13 AI certification here and now work as a VAPT specialist. The course is perfectly designed for Pune’s growing cyber security demand. Real projects, weekly doubt sessions, and excellent placement record – worth every rupee!"

"The CEH v13 AI course in Pune gave me real-world penetration testing skills and hands-on labs that no other institute offers. Got placed at TCS within 2 months of completion. Best decision for my cybersecurity career!"

"Excellent CEH v13 AI training with industry experts. The practical labs and real attack scenarios helped me crack interviews easily. Strong placement support in Pune – highly recommended for anyone serious about ethical hacking!"

"From zero knowledge to landing a penetration testing role – all thanks to Ethical Hacking Institute Pune. The CEH v13 AI curriculum is updated, trainers are exceptional, and the projects gave me confidence to handle real client VAPT work."

"The best cybersecurity training institute in Pune! The CEH v13 AI program covered everything from basic networking to advanced ethical hacking. Placement team helped me secure a SOC Analyst role. 100% practical and job-oriented."

"Transformed my career! The hands-on labs and OSCP-level exposure in the CEH v13 AI course were outstanding. Got multiple offers in Pune’s cybersecurity market. Trainers are industry veterans – truly the best ethical hacking institute."

"I completed the CEH v13 AI certification here and now work as a VAPT specialist. The course is perfectly designed for Pune’s growing cyber security demand. Real projects, weekly doubt sessions, and excellent placement record – worth every rupee!"
Discover why experienced red teamers across Pune trust us for the most advanced EDR/AV evasion program with real enterprise EDR environments and cutting-edge bypass techniques.
Discover how our Ethical Hacking Training Institute stands out, delivering top-tier education for your IT career.







| Date | Mode | Batch | Time | Status | Action |
|---|---|---|---|---|---|
| Sunday, April 19, 2026 | Online/Classroom | Weekdays | 6:30 PM IST | Batch Full | Closed → |
| Sunday, April 26, 2026 | Online/Classroom | Weekdays | 6:30 PM IST |
Only 1 Seat
Max intake limit is 10
|
Enroll Now → |
| Sunday, May 3, 2026 | Online/Classroom | Weekdays | 6:30 PM IST |
5 Seats Left
Max intake limit is 10
|
Enroll Now → |
| Saturday, April 18, 2026 | Online/Classroom | Weekends | 10:00 AM IST |
2 Seats Left
Max intake limit is 10
|
Enroll Now → |
Mode: Online/Classroom
Batch: Weekdays
Time: 6:30 PM IST
Batch FullMode: Online/Classroom
Batch: Weekdays
Time: 6:30 PM IST
Only 1 SeatMode: Online/Classroom
Batch: Weekdays
Time: 6:30 PM IST
5 Seats LeftMode: Online/Classroom
Batch: Weekends
Time: 10:00 AM IST
2 Seats LeftOur EDR/AV Evasion Techniques Training in Pune is the most advanced program focused on bypassing modern Endpoint Detection and Response (EDR) and Antivirus (AV) solutions. You will master process injection, AMSI/ETW bypass, custom loaders, kernel-level evasion, living-off-the-land techniques, and real-world red team evasion strategies using enterprise-grade EDR environments.
Designed for experienced penetration testers and red team operators who want to master the latest EDR/AV bypass techniques. This program is perfect for professionals in Pune ready to operate at the highest level of offensive security. It is ideal for:
Strong penetration testing or red team experience, solid Windows internals knowledge, and advanced scripting skills (C#/PowerShell) are required. This is an advanced-level course.
Understand the foundations of information security, ethical hacking fundamentals, essential controls, relevant laws, and standard security procedures used across the industry.
Discover techniques for gathering target information using search engines, internet research services, social networking sites, WHOIS, DNS, network/email footprinting, social engineering, and advanced tools including AI, along with effective countermeasures.
Master network scanning concepts, tools, host/port/service/OS discovery, scanning beyond IDS and firewalls, source port manipulation, and network scanning countermeasures.
Learn enumeration concepts and techniques for NetBIOS, SNMP, LDAP, NTP, NFS, SMTP, DNS, and other protocols, along with practical countermeasures.
Explore vulnerability assessment concepts, scoring systems, databases, the vulnerability-management life cycle, research, scanning tools, analysis, and professional reporting.
Understand the complete system hacking process: gaining access, escalating privileges, maintaining access, and clearing logs to cover tracks.
Study malware concepts including APTs, trojans, viruses, worms, fileless malware, and AI-based malware, along with comprehensive countermeasures and anti-malware solutions.
Learn sniffing concepts, techniques, popular tools, and effective countermeasures to protect against network traffic interception.
Understand social engineering concepts and techniques (human-based, computer-based, and mobile-based) with practical countermeasures.
Examine DoS/DDoS concepts, botnets, real-world case studies, attack techniques, and robust countermeasures.
Learn session hijacking concepts, application-level and network-level techniques, tools, and effective countermeasures.
Understand IDS/IPS, firewall, and honeypot concepts, evasion techniques, NAC/endpoint security bypass, and corresponding countermeasures.
Explore web server concepts, common attacks, attack methodologies, countermeasures, and patch management strategies.
Learn web application concepts, threats, hacking methodologies, web APIs, webhooks, and essential security measures.
Master SQL injection concepts, types, methodologies, evasion techniques, and strong countermeasures.
Understand wireless concepts, encryption standards, threats, hacking methodologies, and effective countermeasures.
Explore mobile platform attack vectors, hacking techniques for Android and iOS, mobile device management, security guidelines, and essential tools.
Dive into IoT and Operational Technology (OT) concepts, attack vectors, hacking methodologies, and security considerations.
Learn cloud computing concepts, container and serverless technology, hacking methodologies for AWS, Microsoft Azure, and Google Cloud, plus container security and overall cloud security best practices.
Understand cryptography concepts, encryption algorithms, real-world applications, cryptanalysis techniques, and effective countermeasures against cryptographic attacks.
Develop a system that uses machine learning algorithms to identify and block phishing emails in real-time. The project focuses on training AI models to detect malicious URLs, spoofed domains, and suspicious email patterns commonly used in cyberattacks.
Build a tool that leverages AI to analyze and classify malware samples based on their behavior and code signatures. This project emphasizes automating the detection of zero-day vulnerabilities and improving response time to potential threats.
Create a network monitoring system that utilizes AI to detect anomalies in traffic patterns indicative of potential cyberattacks, such as DDoS, brute force, or data exfiltration attempts. The project includes real-time alerts and detailed logging for incident response.
Design a framework that integrates AI to scan and identify vulnerabilities in web applications or systems. The AI module will prioritize high-risk vulnerabilities and simulate potential exploitation scenarios to test system defenses.
Develop an intelligent cloud security platform that uses AI to predict and mitigate threats across AWS, Azure, and Google Cloud environments. The project includes automated misconfiguration detection, anomaly-based breach prediction, and real-time response automation.
In the EDR/AV Evasion Techniques Training in Pune, you gain expert-level command of the same tools and techniques used by top red teams and advanced persistent threats. You will work extensively with Cobalt Strike, Sliver, Donut, SharpShooter, custom shellcode loaders, kernel drivers, and real EDR/AV lab environments.
Our EDR/AV Evasion Techniques certification proves you have mastered the complete process of bypassing modern endpoint protection solutions. This elite credential is globally respected and demonstrates the advanced skills top red teams and offensive security organizations demand.
The EDR/AV Evasion Techniques certification is your proof of elite readiness for modern endpoint bypass operations and gives you a powerful advantage in Pune’s competitive advanced offensive security job market.

The Certified Ethical Hacker (CEH v13) AI Course includes two official certification exams — a theory-based MCQ exam and a hands-on practical exam. Both are designed to validate your real-world ethical hacking and cybersecurity skills.
| Particulars | CEH v13 (MCQ Exam) | CEH v13 (Practical Exam) |
|---|---|---|
| Certification Name | CEH v13 (MCQ Exam) | CEH v13 (Practical Exam) |
| Exam Name | CEH v13 AI | - |
| Exam Format | Multiple Choice Questions | iLabs Cyber Range |
| Interactive Exam Format | Interactive Multiple Choice Questions | - |
| Number of Questions | 125 Questions | 20 Questions |
| Exam Duration | 240 Minutes | 360 Minutes |
| Exam Fee | Varies by country (₹30,000 + 18% GST for India) | - |
| Passing Score | 60-80% | 70% |
| Validity | 3 years | |
| Exam Code | 312-50 (ECC EXAM), 312-50 (VUE) | - |
| Eligibility/Prerequisite | None | |
| Exam Delivery | VUE / ECCEXAM | - |
| Exam Languages | English, Japanese, Korean, and Simplified Chinese | |
You will receive the globally recognized CEH v13 certification only after successfully completing the training, practical projects, and passing the required exam(s). This credential is highly respected by top employers worldwide and adds strong value to your cybersecurity career.
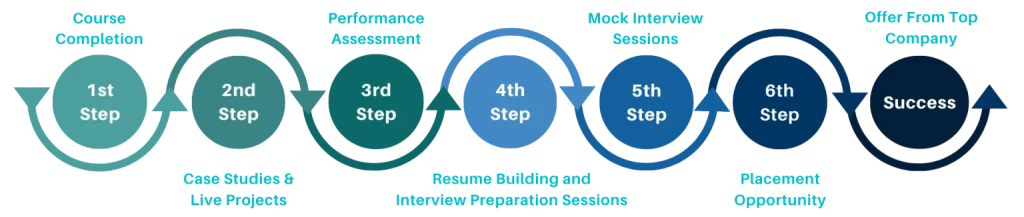
Pune’s defense, fintech, and large enterprise clients require specialists who can bypass the latest EDR/AV solutions. Companies in Kharadi, Hinjewadi, Baner, Viman Nagar and Hadapsar actively seek professionals with proven EDR/AV evasion expertise. Our training includes dedicated placement support, resume building, and technical interview preparation so you can confidently land elite roles.
With complete EDR/AV Evasion Techniques skills, you become one of the most valuable offensive security specialists. Pune’s high-security enterprises offer premium compensation for professionals who can reliably bypass modern endpoint protection.
| Job Profile | Role Description | Average Salary in Pune (INR) |
|---|---|---|
| EDR/AV Evasion Specialist | Develop and execute advanced bypass techniques against enterprise EDR/AV. | Experienced: ₹18L – ₹35L+ |
| Advanced Red Team Operator | Lead red team operations with focus on EDR/AV evasion. | Experienced: ₹22L – ₹45L+ |
| Offensive Security Researcher | Research and develop new EDR/AV evasion methods and implants. | Experienced: ₹20L – ₹40L+ |
| Custom Implant Developer | Build custom loaders, C2 frameworks, and evasion tools. | Experienced: ₹25L – ₹48L+ |
| Red Team Evasion Architect | Design enterprise-grade evasion strategies and toolkits. | Senior: ₹28L – ₹50L+ |
| Elite Penetration Tester | Perform high-end assessments requiring advanced EDR/AV bypass. | Experienced: ₹16L – ₹32L+ |
Key Notes:
Our trainers are active advanced red team operators with proven expertise in bypassing enterprise EDR/AV solutions. They regularly develop custom evasion tools and conduct high-stakes red team operations for government and enterprise clients.
Our trainers ensure you not only learn the techniques but also develop production-grade evasion capabilities used by top red teams.
EDR/AV Evasion Techniques represent one of the most critical and highest-paying specializations in modern offensive security. They prove you can bypass the defenses that protect the world’s largest organizations — exactly what top companies in Pune are looking for.
EDR/AV Evasion Techniques positions you as an elite offensive security professional ready to take on the most challenging and highest-paying roles in Pune’s cybersecurity landscape.
Ethical Hacking Institute Pune is the preferred destination for professionals seeking the most advanced EDR/AV evasion training. We are one of the few institutes that provides intensive, real-world EDR/AV bypass training with live enterprise EDR environments and custom implant development under one roof.
Join the EDR/AV Evasion Techniques program today and get the elite training, expert guidance, and placement support you need to master modern endpoint bypass operations.
Ethical Hacking Institute Pune offers customized EDR/AV Evasion Techniques corporate training programs with intensive hands-on labs using real enterprise EDR/AV solutions. Perfect for organizations in Maharashtra that want their red team and offensive security capabilities to stay ahead of modern endpoint protection.
Strengthen your organization’s red team capabilities with EDR/AV Evasion Techniques corporate training in Pune.